
If you’re in charge of cybersecurity for a United States government agency, you’re already familiar with Memorandum M-22-09, “Moving the U.S. Government Toward Zero Trust Cybersecurity Principles,” which the US Office of Management and Budget issued in January 2022. This memo set a September 30, 2024, deadline for meeting “specific cybersecurity standards and objectives” toward implementing a Zero Trust architecture in compliance with the Executive Order on Improving the Nation’s Cybersecurity.
Microsoft has embraced Zero Trust principles, both in our security products and in the way we secure our own enterprise environment. We’ve been helping thousands of organizations worldwide transition to a Zero Trust security model, including military departments and civilian agencies. Over the past three years, we’ve listened to our US government customers, so we can build rich new security features that help them meet the requirements described in the Executive Order, and then support their deployments. These advancements include certificate-based authentication in the cloud, Conditional Access authentication strength, cross-tenant access settings, FIDO2 provisioning APIs, Azure Virtual Desktop support for passwordless authentication, and device-bound passkeys.
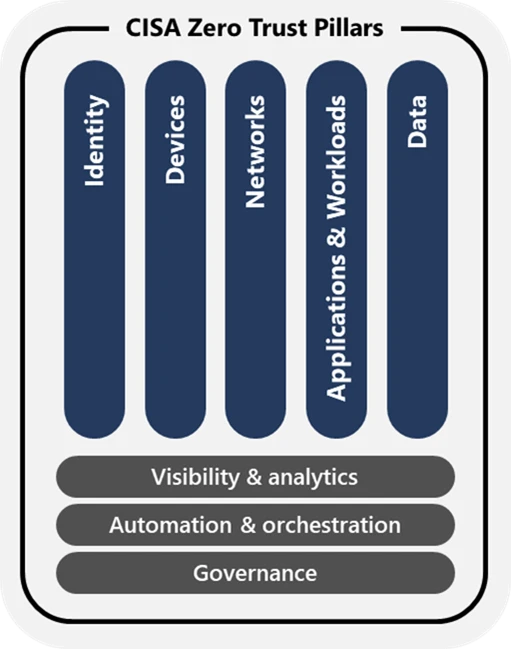
The illustration below depicts the Zero Trust Maturity Model Pillars adopted by the US Cybersecurity and Infrastructure Security Agency (CISA).
As the memo’s deadline approaches, we’d like to celebrate the progress our customers have made using the capabilities in Microsoft Entra ID not only to meet requirements for the Identity pillar, but also to reduce complexity and to improve the user experience for their employees and partners.
Microsoft Entra ID is helping US government customers meet the M-22-09 requirements for identity
US government agencies are adopting Microsoft Entra ID to consolidate siloed identity solutions, reduce operational complexity, and improve control and visibility across all their users, as the memo requires. With Microsoft Entra ID, agencies can enforce multifactor authentication at the application level for more granular control. They can also strengthen security by enabling phishing-resistant authentication for staff, contractors, and partners, and by evaluating device information before authorizing access to resources.
Vision:
Agency staff use enterprise-managed identities to access the applications they use in their work. Phishing-resistant multifactor authentication protects those personnel from sophisticated online attacks.
Actions:
- Agencies must employ centralized identity management systems for agency users that can be integrated into applications and common platforms.
- Agencies must use strong multifactor authentication throughout their enterprise.
- Multifactor authentication must be enforced at the application layer, instead of the network layer.
- For agency staff, contractors, and partners, phishing-resistant multifactor authentication is required.
- For public users, phishing-resistant multifactor authentication must be an option.
- Password policies must not require use of special characters or regular rotation.
- When authorizing users to access resources, agencies must consider at least one device-level signal alongside identity information about the authenticated user.
Source: M-22-09: Moving the US Government Toward Zero Trust Cybersecurity Principles, issued by the US Office of Management and Budget, January 2022, page 5.
Many of our US government civilian and military customers want to use the same solutions across their different environments. Since it’s available in secret and top-secret Microsoft Azure Government clouds, agencies can standardize on Microsoft Entra ID to secure user identities, to configure granular access permissions in one place, and to provide simpler, easier, and more secure sign-in experiences to applications their employees use in their work.
Microsoft Entra ID
Establish Zero Trust access controls, prevent identity attacks, and manage access to resources.

Using Microsoft Entra ID as a centralized identity management system
Anyone who has struggled to manage multiple identity systems understands that it’s an expensive and inefficient approach. Government customers who have adopted Microsoft Entra ID as their central agency identity provider (IdP) gained a holistic view of all users and their access permissions as required by the memo. They also gained a centralized access policy engine that combines signals from multiple sources, including identities and devices, to detect anomalous user behavior, assess risk, and make real-time access decisions that adhere to Zero Trust principles.
Moreover, Microsoft Entra ID enables single sign-on (SSO) to resources and apps, including apps from Microsoft and thousands of other vendors, whether they’re on-premises or in Microsoft commercial or government clouds. When deployed as the central agency IdP, Microsoft Entra ID also secures access to resources in clouds from Amazon, Google, and Oracle.
Many government customers are facilitating secure collaboration among different organizations by using Microsoft Entra External ID for business-to-business (B2B) collaboration to enable cross-cloud access scenarios. They don’t have to give collaboration partners separate credentials for accessing applications and documents in their environment, which reduces their cyberattack surface and spares their partner users from maintaining multiple sets of credentials for multiple identity systems.
Using Microsoft Entra ID to facilitate cross-organizational collaboration
Cross-tenant access with Microsoft Entra External ID
One of our government customers, along with their partner agency, configured cross-tenant access settings to trust multifactor authentication claims from each user’s home tenant. Their partner agency can now trust and enforce strong phishing-resistant authentication for the customer’s users without forcing them to sign in multiple times to collaborate. The partner agency also explicitly enforces, through a Conditional Access authentication strength policy, that the customer’s users must sign in using a personal identity verification (PIV) card or a common access card (CAC) before gaining access.
Configure cross-tenant access settings for B2B collaboration
Another government customer needed to give employees from different organizations within the same agency access to shared services applications such as human resources systems. They used Microsoft Entra External ID for B2B collaboration along with cross-cloud settings to enable seamless and secure collaboration and resource sharing for all agency employees, other government agencies (OGAs), and external partners. They used Microsoft Entra Conditional Access policy and cross-tenant access settings to require that employees sign in using phishing-resistant authentication before accessing shared resources. Trust relationships ensure that this approach works whether the home tenant of an employee is in an Azure commercial or government cloud. They also enabled collaboration with agencies that use an IdP other than Microsoft Entra ID by setting up federation through the SAML 2.0 and WS-Fed protocols.
Next step after standardizing on Microsoft Entra ID as your centralized IdP: Use Microsoft Entra ID Governance to automate lifecycle management of guest accounts in your tenant, so guest users only get access to the resources they need, for only as long as they need it. Start here: What are lifecycle workflows?
Enabling strong multifactor authentication
Standardizing on Microsoft Entra ID has made it possible for our government customers to enable phishing-resistant authentication methods. Over the past 18 months, we’ve worked with our US government customers to increase adoption of phishing-resistant multifactor authentication with Microsoft Entra by almost 2,000%.
From there, customers configure Conditional Access policies that require strong phishing-resistant authentication for accessing applications and resources, as required by the memo. Using Conditional Access authentication strength, they can even set policies to require additional, stronger authentication based on the sensitivity of the application or resource the user is trying to access, or the operation they’re trying to perform.
Microsoft Entra supports strong phishing-resistant forms of authentication:
- Certificate-based authentication (CBA) using Personal Identification Cards (PIV) or Common Access Cards (CAC)
- Device-bound passkeys
- FIDO2 security keys
- Passkeys in the Microsoft Authenticator app
- Windows Hello for Business
- Platform single sign-on SSO for macOS devices (in preview)
For a deep dive into phishing resistant authentication in Microsoft Entra, explore the video series Phishing-resistant authentication in Microsoft Entra ID.
While Microsoft Entra ID can prevent the use of common passwords, identify compromised passwords, and enable self-service password reset, many of our government customers prefer to require the most secure forms of authentication, such as smart cards with x.509 certificates and passkeys, which don’t involve passwords at all. This makes signing in more secure, simplifies the user experience, and reduces management complexity.
Implementing phishing-resistant multifactor authentication methods with Microsoft Entra ID
Migrate to cloud authentication using Staged Rollout
To reduce the cost and complexity of maintaining an on-premises authentication infrastructure using Active Directory Federation Services (AD FS) for employee PIV cards, one agency wanted to use certificate-based authentication (CBA) in Microsoft Entra ID. To ensure the transition went smoothly, they moved users with Staged Rollout, carefully monitoring threat activity using Microsoft Entra ID Protection dashboards and Microsoft Graph API logs exported to their security information and event management (SIEM) system. They migrated all their users to cloud-based CBA in Microsoft Entra in less than three months and after monitoring the environment for a time, confidently decommissioned their AD FS servers.
Public preview: Microsoft Entra ID FIDO2 provisioning APIs
A local government department chose an opt-in approach for moving employees and vendors to phishing-resistant authentication. Every user contacting the help desk for a password reset instead received help onboarding to Windows Hello for Business. This agency also gave FIDO2 keys to all admins and set a Conditional Access authentication strength policy requiring all vendors to perform phishing-resistant authentication. Their next step will be to roll out device-bound passkeys managed in the Microsoft Authenticator app and enforce their use through Conditional Access. This will save them the expense of issuing separate physical keys and give their users the familiar experience of authenticating securely from their mobile device.
Supported identities and authentication methods in Azure Virtual Desktop
By giving users access to applications and resources through Azure Virtual Desktop, another large agency avoids the overhead of maintaining and supporting individual devices and the software running on them. They also protect their environment from potentially unhealthy, misconfigured, or stolen devices. Whether employees use devices running Windows, MacOS, iOS, or Android, they run the same Virtual Desktop image and sign in, as policy requires, using phishing-resistant, passwordless authentication.
Next step after enabling strong multifactor authentication: Configure Conditional Access authentication strength to enforce phishing-resistant authentication for accessing sensitive resources. Start here: Overview of Microsoft Entra authentication strength.
Using Conditional Access policies to authorize access to resources
Using Conditional Access, our government customers have configured fine-tuned access policies that consider contextual information about the user, their device, their location, and real-time risk levels to control which apps and resources users can access and under what conditions.
To satisfy the memo’s third identity requirement, these customers include device-based signals in policies that make authorization decisions. For example, Microsoft Entra ID Protection can detect whether a device’s originating network is safe or unsafe based on its geographic location, IP address range, or whether it’s coming from an anonymous IP address (for example, TOR). Conditional Access can evaluate signals from Microsoft Intune or other mobile device management systems to determine whether a device is properly managed and compliant before granting access. It can also consider device threat signals from Microsoft Defender for Endpoint.
Enabling Microsoft Entra Conditional Access risk-based policies
One government department enabled risk-based Conditional Access policies across their applications, requiring more stringent sign-in methods depending on levels of user and sign-in risk. For example, a user evaluated as ‘no-risk’ must always perform multifactor authentication, a user evaluated as ‘low-medium risk’ must sign in using phishing-resistant multifactor authentication, and a user deemed ‘high-risk’ must sign in using a specific certificate issued to them by the department. The customer has also configured policy to require compliant devices, enable token protection, and define sign-in frequency. To facilitate threat hunting and automatic mitigation, they send their sign-in and other Microsoft Entra logs to Microsoft Sentinel.
Next step after configuring basic Conditional Access policies: Configure risk-based Conditional Access policies using Microsoft Intune. Start here: Configure and enable risk policies.
Next steps
On July 10, 2024, the White House issued Memorandum M-21-14, “Administration Cybersecurity Priorities for the FY 2026 Budget.” One budget priority calls on agencies to transition toward fully mature Zero Trust architectures by September 30, 2026. Agencies need to submit an updated implementation plan to the Office of Management and Budget within 120 days of the memo’s release. Agencies in the Department of Defense must also implement Zero Trust by September 30, 2026, a year earlier than the previously published timeline.
Microsoft is here to help you rearchitect your environment and implement your Zero Trust strategy, so you can comply with every milestone of the Executive Order. We’ve published technical guidance and detailed documentation to help federal agencies use Microsoft Entra ID to meet identity requirements. We’ve also published detailed guidance on meeting the Department of Defense Zero Trust requirements with Microsoft Entra ID.
In the coming weeks and months, you’ll see announcements about additional steps we’re taking to simplify your Zero Trust implementation, such as the general availability of support for device-bound passkeys in Microsoft Authenticator and Microsoft-managed Conditional Access policies that enable multifactor authentication by default for US government customers.
We look forward to supporting you through the next phases of your Zero Trust journey.
- Standardize on Microsoft Entra ID as your centralized identity provider to secure every identity and to secure access to your apps and resources. Start here: What is Microsoft Entra ID?
- To facilitate secure cross-organization collaboration, configure cross-tenant access settings and Conditional Access policies to require that partners accessing your resources sign in using phishing-resistant authentication. Start here: Microsoft Entra B2B in government and national clouds.
- If you’re using CBA on AD FS, migrate to cloud-based CBA using Staged Rollout and retire your on-premises federation servers. Start here: Migrate from AD FS Certificate-based Authentication (CBA) to Microsoft Entra ID CBA.
- Eliminate passwords altogether by enabling passwordless phishing-resistant authentication using CBA, Windows Hello for Business, device-bound passkeys (FIDO2 security keys or passkeys managed in the Microsoft Authenticator app), or Platform SSO for MacOS. Start here: Plan a passwordless authentication deployment in Microsoft Entra ID.
- Implement risk-based Conditional Access policies to adjust access requirements dynamically. Start here: DoD Zero Trust Strategy for the user pillar.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.