

The FBI announced on Monday that it seized the servers and websites of the Radar/Dispossessor ransomware operation following a joint international investigation.
The joint operation was carried out in collaboration with the U.K.’s National Crime Agency, the Bamberg Public Prosecutor’s Office, and the Bavarian State Criminal Police Office (BLKA).
Law enforcement seized three U.S. servers, three U.K. servers, 18 German servers, eight U.S.-based domains, and one German-based domain, including radar[.]tld, dispossessor[.]com, cybernewsint[.]com (fake news site), cybertube[.]video (fake video site), and dispossessor-cloud[.]com.
Since August 2023, Dispossessor—led by a threat actor known as Brain—has targeted small to mid-sized businesses in various sectors worldwide, claiming attacks against dozens of companies (the FBI identified 43 victims) from the U.S., Argentina, Australia, Belgium, Brazil, Honduras, India, Canada, Croatia, Peru, Poland, the United Kingdom, the United Arab Emirates, and Germany.
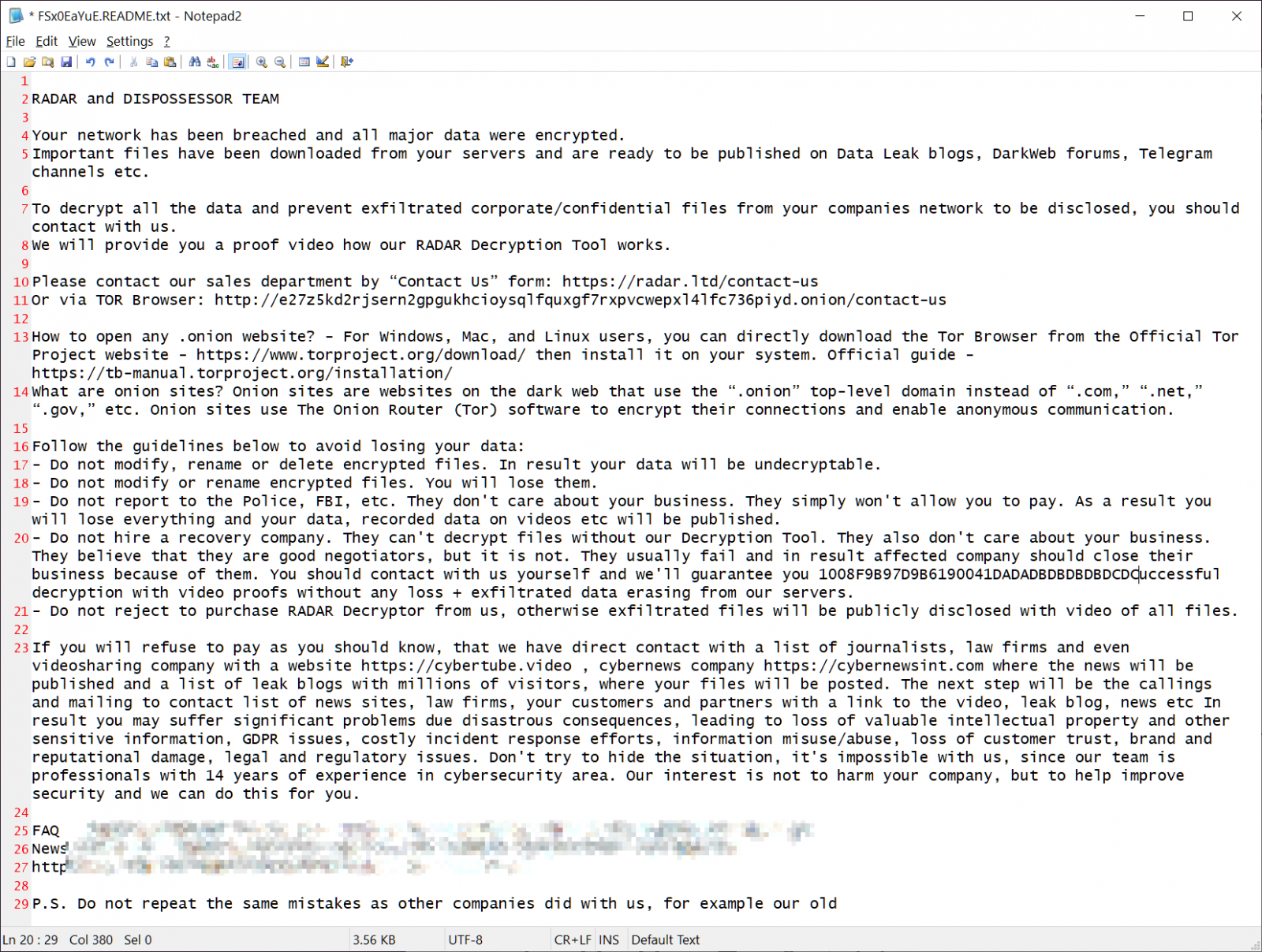
The FBI says the ransomware gang breaches networks through vulnerabilities, weak passwords, and the lack of multi-factor authentication configured on accounts. After gaining access to the victim’s network, they steal data and deploy the ransomware to encrypt the company’s devices.
“Once the criminals gained access to the systems, they obtained administrator rights and easily gained access to the files. The actual ransomware was then used for encryption. As a result, the companies could no longer access their own data,” the FBI said in a press release shared with BleepingComputer.
“Once the company was attacked, if they did not contact the criminal actor, the group would then proactively contact others in the victim company either through email or phone call. The emails also included links to video platforms on which the previously stolen files had been presented.”
The FBI also asked past victims or those targeted to share information on the Dispossessor gang by contacting the Internet Crime Complaint Center at ic3.gov or 1-800-CALL FBI.
When the cybercrime group initially launched, it acted as an extortion group, reposting old data stolen during LockBit ransomware attacks, from which they claimed to be affiliates. Dispossessor has also been reposting leaks from other ransomware operations and attempting to sell them on various breach markets and hacking forums like BreachForums and XSS.
“Dispossessor initially announced the renewed availability of the data from some 330 LockBit victims. This was claimed to be reposted data from previously available LockBit victims, now hosted on Dispossessor’s network and thus not subject to LockBit’s availability restrictions,” SentinelOne said in an April report.
“Dispossessor appears to be reposting data previously associated with other operations with examples ranging from Cl0p, Hunters International, and 8base. We are aware of at least a dozen victims listed on Dispossessor that have also been previously listed by other groups.”
Starting in June 2024, the threat actors began utilizing the leaked LockBit 3.0 encryptor [VirusTotal] for use in their own encryption attacks, significantly escalating the scope of their attacks.
Over the past year, law enforcement operations have targeted many other cybercrime activities, including cryptocurrency scams, malware development, phishing attacks, credential theft, and ransomware operations.
For instance, they have used hack-back tactics to infiltrate, disrupt, and dismantle ALPHV/Blackcat ransomware, a ransomware group deploying LockerGoga, MegaCortex, HIVE, and Dharma, the Ragnar Locker ransomware operation, and Hive ransomware.