

Fake AI image and video generators infect Windows and macOS with the Lumma Stealer and AMOS information-stealing malware, used to steal credentials and cryptocurrency wallets from infected devices.
Lumma Stealer is a Windows malware and AMOS is for macOS, but both steal cryptocurrency wallets and cookies, credentials, passwords, credit cards, and browsing history from Google Chrome, Microsoft Edge, Mozilla Firefox, and other Chromium browsers.
This data is collected into an archive and sent back to the attacker, where they can use the information in further attacks or sell it on cybercrime marketplaces.
Fake AI image generators push Lumma Stealer
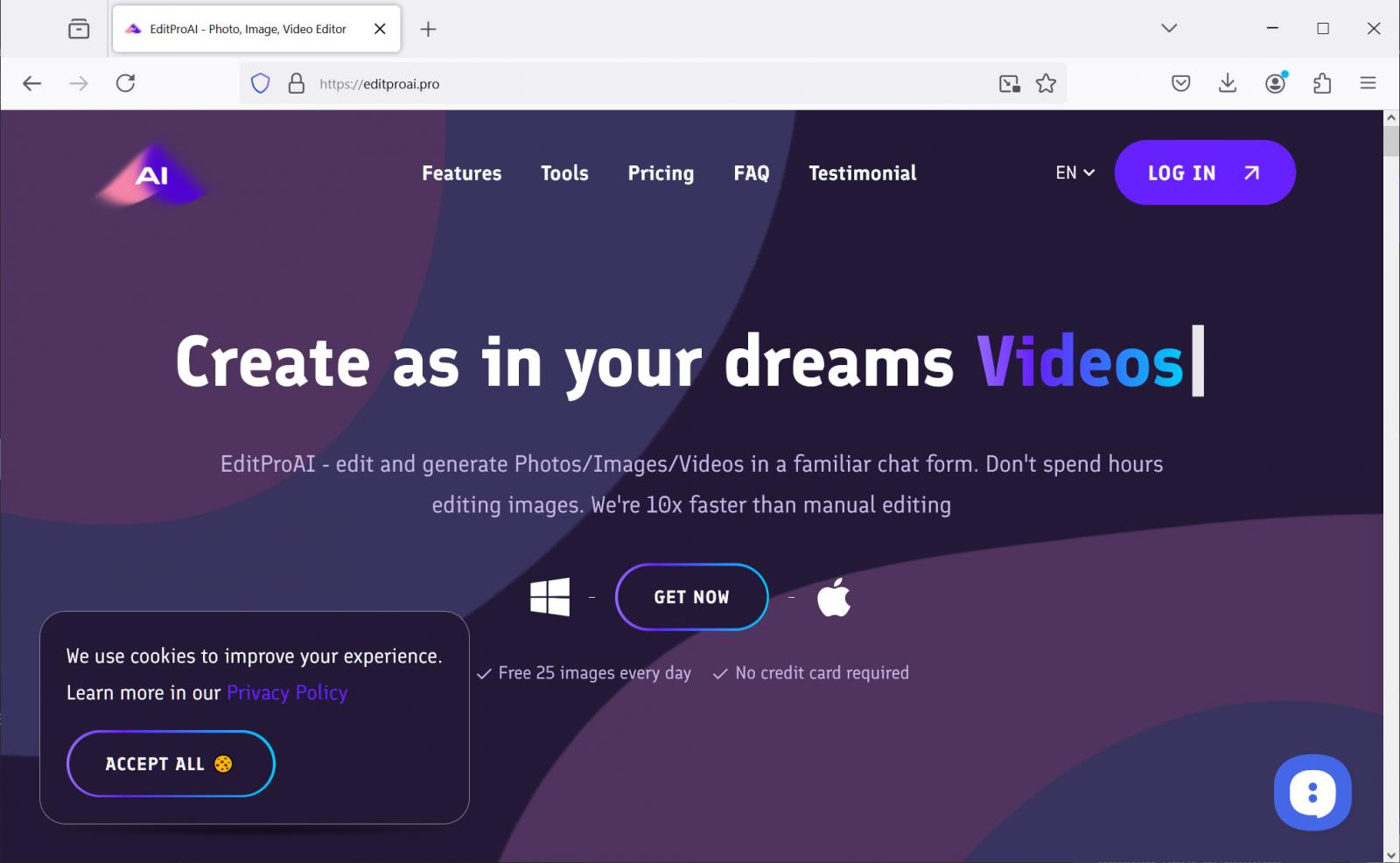
Over the past month, threat actors have created fake websites that impersonate an AI video and image editor called EditPro.
As discovered by cybersecurity researcher g0njxa, the sites are promoted through search results and advertisements on X that share deepfake political videos, such as President Biden and Trump enjoying ice cream together.

Source: BleepingComputer.com
Clicking the images brings you to fake websites for the EditProAI application, with editproai[.]pro created to push Windows malware and editproai[.]org to push macOS malware.
The sites are professional-looking and even contain the ubiquitous cookie banner, making them look and feel legitimate.
Source: BleepingComputer
However, clicking the “Get Now” links will download an executable pretending to be the EditProAI application. For Windows users, the file is called “Edit-ProAI-Setup-newest_release.exe” [VirusTotal] and for macOS, it is named “EditProAi_v.4.36.dmg” [VirusTotal].
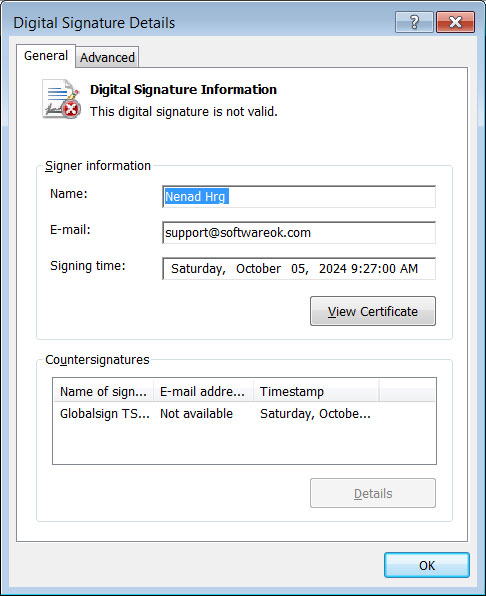
The Windows malware is signed by what appears to be a stolen code signing certificate from Softwareok.com, a freeware utility developer.
Source: BleepingComputer
G0njxa says that malware uses a panel at “proai[.]club/panelgood/” to send stolen data, which can then be retrieved at a later time by the threat actors.
An AnyRun report shows the execution of the Windows variant, with the sandbox service detecting the malware as Lumma Stealer.
If you have downloaded this program in the past, you should consider all of your saved passwords, cryptocurrency wallets, and authentications compromised and immediately reset them with unique passwords at every site you visit.
You should also enable multi-factor authentication at all sensitive sites, such as cryptocurrency exchanges, online banking, email services, and financial services.
Information-stealing malware has seen massive growth over the last few years, with threat actors conducting massive global operations to steal people’s credentials and authentication tokens.
Other campaigns recently pushing infostealers include the use of zero-day vulnerabilities, fake fixes to GitHub issues, and even fake answers on StackOverflow.
The stolen credentials are then used to breach corporate networks, conduct data theft campaigns like we saw with the massive SnowFlake account breaches, and cause chaos by corrupting network routing information.