

Palo Alto Networks is warning that a critical zero-day vulnerability on Next-Generation Firewalls (NGFW) management interfaces, currently tracked as ‘PAN-SA-2024-0015,’ is actively being exploited in attacks.
The flaw was originally disclosed on November 8, 2024, with Palo Alto Networks warning customers to restrict access to their next-generation firewalls because of a “potential” remote code execution (RCE) vulnerability impacting them.
No signs of exploitation were detected at that time, but now, one week later, the situation has changed.
“Palo Alto Networks has observed threat activity exploiting an unauthenticated remote command execution vulnerability against a limited number of firewall management interfaces which are exposed to the Internet,” warns an update on the advisory page.
“At this time, we believe devices whose access to the Management Interface is not secured as per our recommended best practice deployment guidelines are at increased risk,” warns the vendor in the same bulletin.
The vulnerability, rated with a CVSS v4.0 score of 9.3 (“critical”), is remotely exploitable and requires no authentication or user interaction.
Once an internet-exposed interface is detected, the attacker can send a specially crafted request to gain unauthorized control over the firewall, potentially enabling them to alter rules, redirect or intercept network traffic, and turn off security protections.
Unfortunately, the vendor does not have sufficient information to formulate a useful list of indicators of compromise at this time, but suggested the following mitigation steps:
- Configure access to the firewall management interface so it is only accessible from trusted internal IP addresses.
- Block all internet access to the management interface to prevent exploitation.
- Place the management interface behind a secured network or VPN to ensure access is controlled and authenticated.
- Review and implement the security guidelines found here.
Despite the dangerous RCE bug being discovered a week ago, Palo Alto Networks has not yet made security updates available to impacted clients.
“At this time, securing access to the management interface is the best recommended action,” says Palo Alto Networks.
“As we investigate the threat activity, we are preparing to release fixes and threat prevention signatures as early as possible.”
Threat monitoring platform The Shadowserver Foundation reported earlier today that it sees approximately 8,700 exposed interfaces.
Threat researcher Yutaka Sejiyama conducted his own scans on Shodan and told BleepingComputer that he observed 11,180 IP addresses exposed online associated with the Palo Alto management interface.
“As you know, the results from Shodan are not real-time information. However, during my investigation three days ago, I confirmed that 11,180 of these IPs were actually online,” Sejiyama told BleepingComputer.
According to Shodan, most of the devices are located in the United States, followed by India, Mexica, Thailand, and Indonesia.
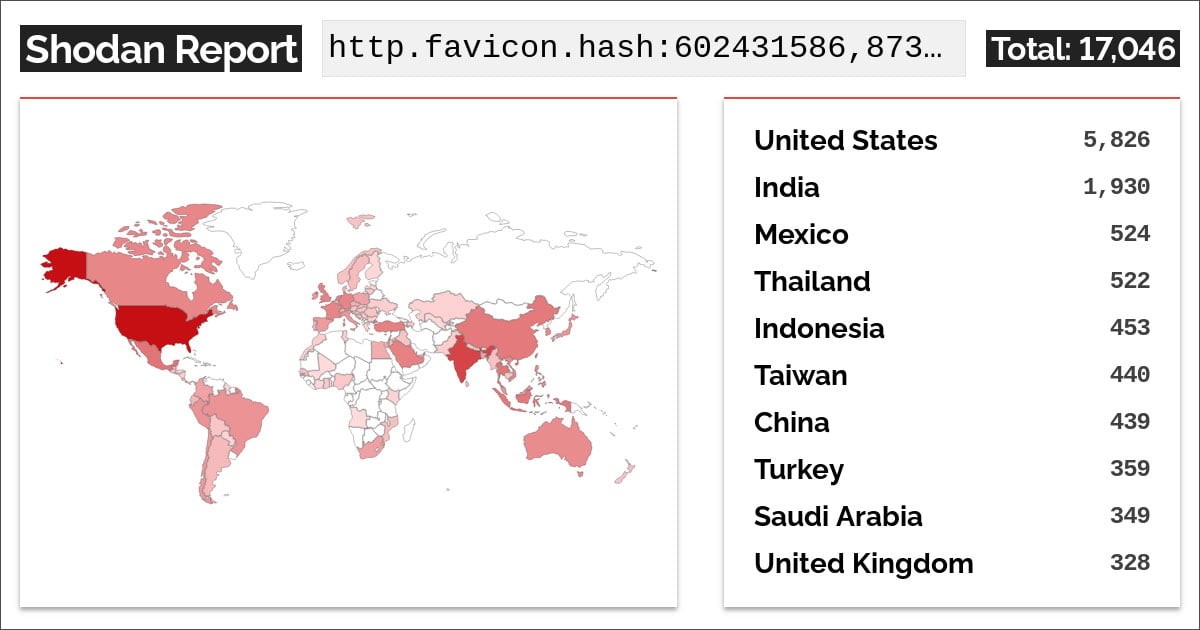
Source: Shodan
To ensure that you have applied the mitigations properly, visit the Assets section of the Palo Alto Networks Customer Support Portal to find a list of devices with Internet-facing management interfaces, and look for devices tagged with ‘PAN-SA-2025-0015.’
If none showed up, the scan did not detect any internet-exposed management interfaces. If they do, admins should use the steps mentioned to secure devices.
