

Cisco says that non-public files recently downloaded by a threat actor from a misconfigured public-facing DevHub portal don’t contain information that could be exploited in future breaches of the company’s systems.
While analyzing the exposed documents, the company found that their contents include data that Cisco publishes for customers and other DevHub users. However, files that shouldn’t have been made public were also available, some belonging to CX Professional Services customers.
“So far, in our research, we’ve determined that a limited set of CX Professional Services customers had files included and we notified them directly,” Cisco said.
“Our teams have indexed and continue assessing the content of those files, and we continue to make steady progress. We have not identified any information in the content that an actor could have used to access any of our production or enterprise environments.”
Cisco has since corrected the configuration, restored public access to the DevHub site, and says that web search engines did not index the exposed documents.
This update comes after Cisco confirmed last month that it took its public DevHub site offline (a resource center for customers where it publishes software code, templates, and scripts) after a threat actor leaked what the company described at the time as “non-public” data.
The company added that it found no evidence that any financial data or personal information had been exposed or stolen from the public DevHub portal before it was taken offline.
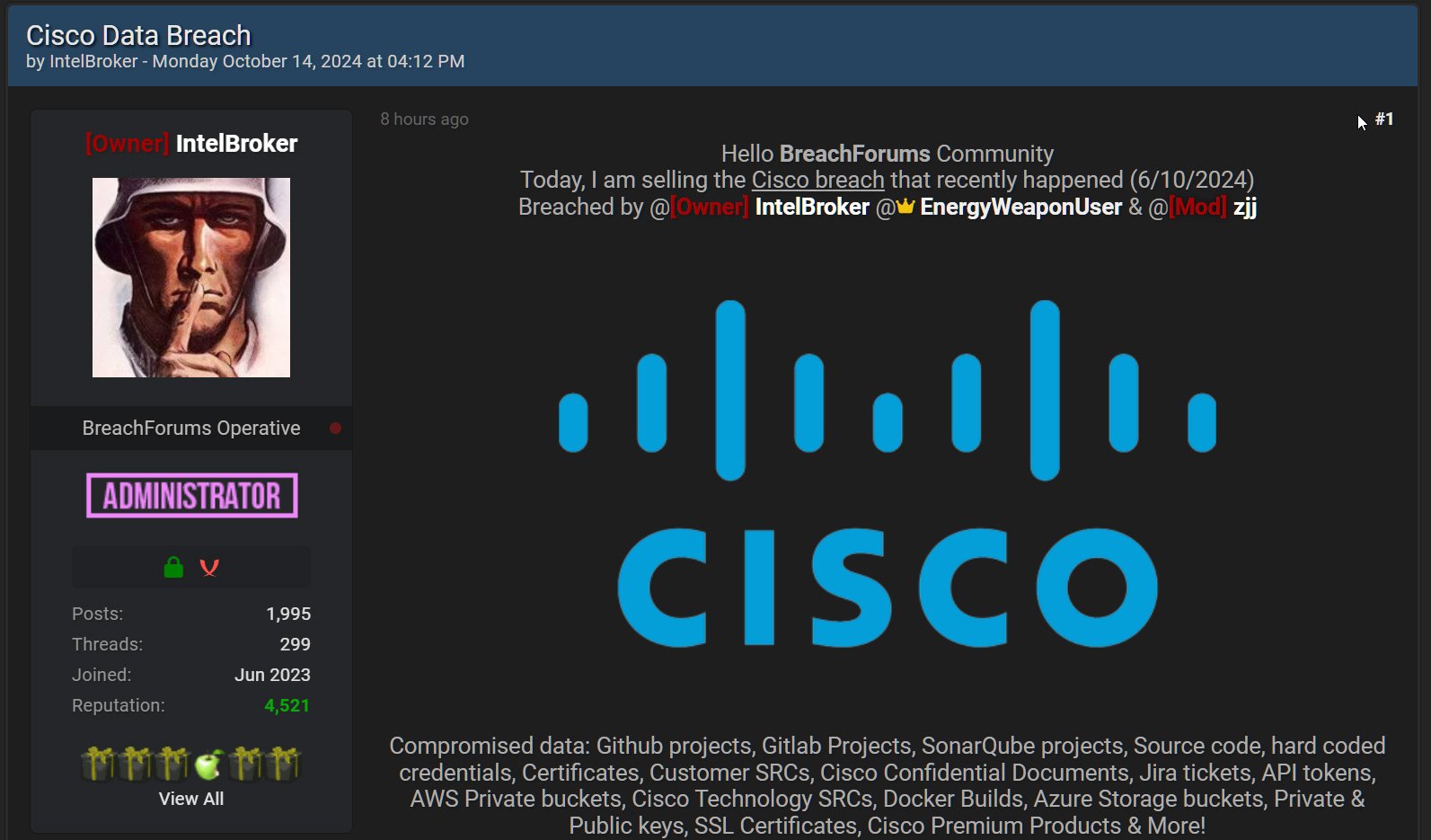
IntelBroker (the threat actor behind the leak) told BeelpingComputer they also allegedly gained access to a Cisco JFrog developer environment through an exposed API token.
Screenshots and files the threat actor shared with BeelpingComputer showed they gained access to source code, configuration files with database credentials, technical documentation, and SQL files.
While Cisco says its systems haven’t been breached, information shared by the threat actor indicates that they also breached a third-party development environment, allowing them to steal data.
BleepingComputer contacted Cisco with further questions about IntelBroker’s claims, but the company has not replied.