

The North Korean hacking group ScarCruft launched a large-scale attack in May that leveraged an Internet Explorer zero-day flaw to infect targets with the RokRAT malware and exfiltrate data.
ScarCruft (aka “APT37” or “RedEyes”) is a state-sponsored cyber-espionage threat actor known for targeting systems in South Korea and Europe, as well as North Korean human rights activists and defectors, using phishing, watering hole, and Internet Explorer zero-days.
A new joint report by South Korea’s National Cyber Security Center (NCSC) and AhnLab (ASEC) outlines a recent ScarCruft campaign dubbed “Code on Toast,” which leveraged toast pop-up ads to perform zero-click malware infections.
The flaw used in zero-day attacks is tracked as CVE-2024-38178 and is a high-severity type confusion flaw in Internet Explorer.
ASEC and NCSC, responding to the campaign, informed Microsoft immediately, and the tech giant released a security update to address CVE-2024-39178 in August 2024.
Interestingly, the researchers found that ScarCruft’s exploit was very similar to the one they used in the past for CVE-2022-41128, with the only addition being three lines of code designed to bypass Microsoft’s previous fixes.
From ‘Toast ads’ to malware
Toast notifications are pop-ups displayed in the corner of software such as antivirus or free utility programs to display notifications, alerts, or advertisements.
According to AhnLab, APT37 compromised one of the servers of a domestic advertising agency to push specially crafted ‘Toast ads’ on an unnamed free software used by a large number of South Koreans.
These advertisements included a malicious iframe that, when rendered by Internet Explorer, caused a JavaScript file named ‘ad_toast,’ to trigger remote code execution via the CVE-2024-39178 flaw in Internet Explorer’s JScript9.dll file (Chakra engine).
The malware dropped in this attack is a variant of RokRAT, which ScarCruft has been using in attacks for several years now.
RokRAT’s primary role is to exfiltrate files matching 20 extensions (including .doc, .mdb, .xls, .ppt, .txt, .amr) to a Yandex cloud instance every 30 minutes.
The malware also performs keylogging, monitors for clipboard changes, and captures screenshots (every 3 minutes).
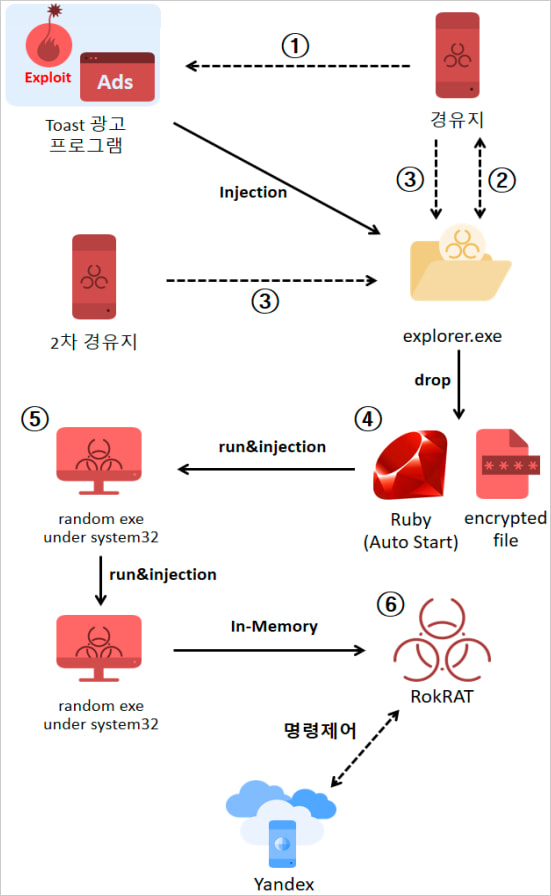
Source: ASEC
The infection is performed via a four-step process where an equal number of payloads are injected into the ‘explorer.exe’ process, evading detection by security tools.
If Avast or Symantec antivirus is detected on the host, the malware is injected into a random executable from the C:\Windows\system32 folder instead.
Persistence is achieved by adding a final payload (‘rubyw.exe’) to the Windows startup and registering it for execution in the system’s scheduler every four minutes.
Despite Microsoft announcing Internet Explorer’s retirement in mid-2022, many of the browser’s components remain in Windows or are used by third-party software, allowing threat actors to discover new vulnerabilities for use in attacks.
This may be happening without the users even realizing they’re on outdated software that can be easily exploited for zero-click attacks, laying the ground for mass-scale exploitation by knowledgeable threat actors.
What makes this worse is that even though Microsoft fixed this particular Internet Explorer flaw in August, it does not guarantee that it will be adopted immediately by tools using older components. Therefore, free software using outdated Internet Explorer components continues to put users at risk.
BleepingComputer asked ASEC about the number of impacted users and the name of the exploited free software, and we will update you with more information once available.